Wordpress <= 4.9.4 - Application Denial Of Service (Dos) (Unpatched) Fix?

A simple yet serious application-level denial of service (DoS) vulnerability has been discovered in WordPress CMS platform that could allow anyone to accept down most WordPress websites even with a unmarried car—without hitting with a massive amount of bandwidth, as required in network-level DDoS attacks to accomplish the same.
Since the company has denied patching the issue, the vulnerability (CVE-2018-6389) remains unpatched and affects about all versions of WordPress released in terminal nine years, including the latest stable release of WordPress (Version iv.9.2).
Discovered by Israeli security researcher Barak Tawily, the vulnerability resides in the way " load-scripts.php ," a born script in WordPress CMS, processes user-defined requests.

For those unaware, load-scripts.php file has but been designed for admin users to assistance a website ameliorate performance and load page faster by combining (on the server end) multiple JavaScript files into a single asking.
Even so, to make "load-scripts.php" work on the admin login folio (wp-login.php) before login, WordPress authors did not go along whatever hallmark in place, eventually making the feature accessible to anyone.
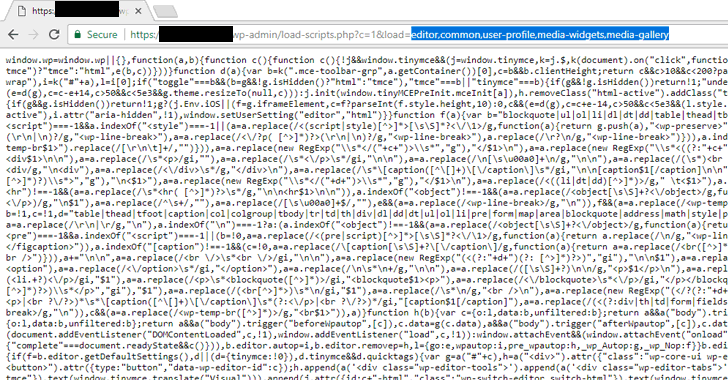
Depending upon the plugins and modules you accept installed, the load-scripts.php file selectively calls required JavaScript files by passing their names into the "load" parameter, separated by a comma, like in the following URL:
https://your-wordpress-site.com/wp-admin/load-scripts.php?c=1&load=editor,common,user-profile,media-widgets,media-gallery
While loading the website, the 'load-scripts.php' (mentioned in the head of the folio) tries to find each JavaScript file name given in the URL, append their content into a single file and so send back it to the user's web browser.
How WordPress DoS Set on Works
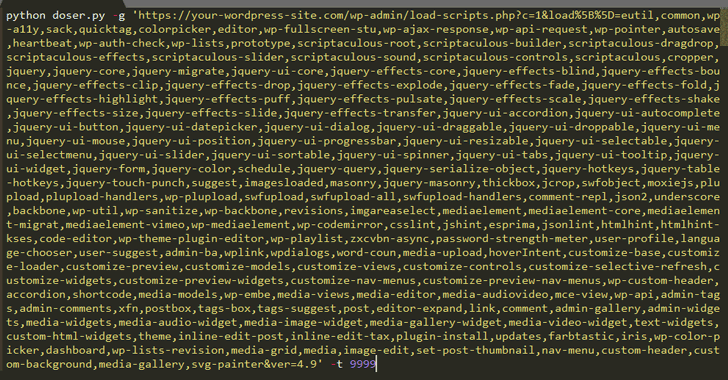
According to the researcher, one tin can but force load-scripts.php to call all possible JavaScript files (i.e., 181 scripts) in one go past passing their names into the to a higher place URL, making the targeted website slightly slow past consuming high CPU and server memory.
"In that location is a well-defined list ($wp_scripts), that can be requested by users equally office of the load[] parameter. If the requested value exists, the server will perform an I/O read activity for a well-defined path associated with the supplied value from the user," Tawily says.
Although a single request would not be enough to take down the whole website for its visitors, Tawily used a proof-of-concept (PoC) python script, doser.py, which makes large numbers of concurrent requests to the same URL in an attempt to use up as much of the target servers CPU resources as possible and bring it down.

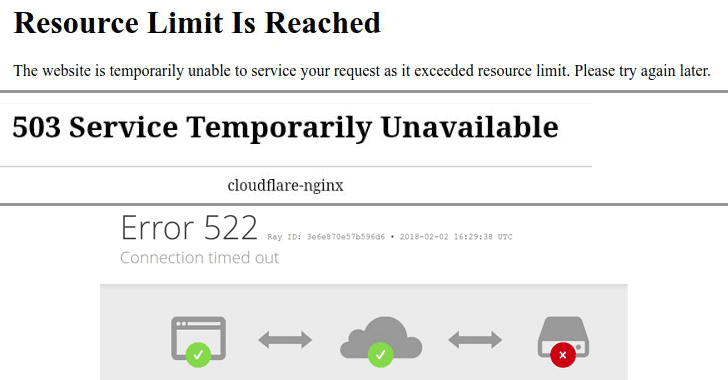
The Hacker News has verified the authenticity of the DoS exploit that successfully took downward one of our demo WordPress websites running on a medium-sized VPS server.
"It is fourth dimension to mention again that load-scripts.php does not require whatever hallmark, an bearding user tin practice so. After ~500 requests, the server didn't respond at all any more, or returned 502/503/504 status code errors," Tawily says.
However, attack from a unmarried motorcar, with some 40 Mbps connectedness, was not plenty to have downwardly another demo website running on a dedicated server with high processing power and retention.
But that doesn't mean the flaw is not effective confronting WordPress websites running over a heavy-server, equally application-level attack by and large requires a lot fewer packets and bandwidth to achieve the same goal—to take downwardly a site.
So attackers with more bandwidth or a few bots tin exploit this flaw to target big and popular WordPress websites as well.
No Patch Available – Mitigation Guide
Along with the full disclosure, Tawily has as well provided a video demonstration for the WordPress Denial of Service attack. You tin watch the video to see the assail in action.
Knowing that DoS vulnerabilities are out-of-scope from the WordPress bug compensation programme, Tawily responsibly reported this DoS vulnerability to the WordPress team through HackerOne platform.
Withal, the company refused to acknowledge the consequence, proverb that this kind of bug "should really get mitigated at the server end or network level rather than the application level," which is outside of WordPress's control.
The vulnerability seems to exist serious considering WordPress powers virtually 29 percentage of the Web, placing millions of websites vulnerable to hackers and making them unavailable for their legitimate users.
For websites that can't afford services offering DDoS protection against awarding-layer attacks, the researcher has provided a forked version of WordPress, which includes mitigation confronting this vulnerability.
Still, I personally wouldn't recommend users to install modified CMS, even if it is from a trusted source other than the original author.
Besides this, the researcher has also released a simple bash script that fixes the consequence, in case you have already installed WordPress.
Found this commodity interesting? Follow THN on Facebook, Twitter and LinkedIn to read more exclusive content nosotros post.
Source: https://thehackernews.com/2018/02/wordpress-dos-exploit.html
Posted by: gutierrezdialt1955.blogspot.com


0 Response to "Wordpress <= 4.9.4 - Application Denial Of Service (Dos) (Unpatched) Fix?"
Post a Comment